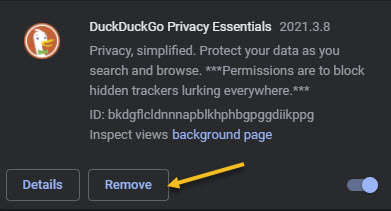
Have you ever noticed the message you see when you install a browser extension in Chrome, for example? For most browser extensions, a message appears stating that the extension can “Read and modify all of your information on the websites you visit.” Refer to below image where we are looking at DuckDuckGo Privacy Essentials extension, an Internet privacy company, on their permissions:

What! Does not look secure to me as it reads all data on your device. You want to remove this browser extension and similar extensions for privacy issues.
To review your Chrome browser extensions:
- Open Chrome, and click the 3-dot hamburger icon in upper-right hand corner.
- Click on More Tools, then Extensions. They will be listed alphabetically.
- Find a browser Extension that is enabled. Click on its Details button. Now, scroll down to the Permissions and Site Access sections to view how it is accessing your data.
You may be surprised as to the information the Extension is collecting on you. Let’s explore what this is about.
This is for modern day browsers like Edge, Chrome, Firefox, and Safari. Screenshots are from Chrome desktop version

This means that the browser extension has full access to all web pages you visit. It can see which web pages you are browsing, read their content and look at everything you write. It can even modify the web pages; for example by inserting additional ads. If the extension is malicious, it can collect all your private information; from web activity and emails you write to your passwords and financial information; and send it to a remote server on the Internet.
I am tired of receiving fake emails, texts, tweets, posts, and so on. Recently I have been receiving media from Thank You, USPS, Wells Fargo, Cox Communications, and so on.
This is primarily due to my accounts being compromised and sold. Another reason is some browser extensions is watching my activity.
If a browser extension is completely reliable and trustworthy, that’s fine. The browser extension may behave responsibly and not capture any data or interfere with your banking information.
We do not say that you have to uninstall every browser extension you have. Instead, you just realize the enormous access you give to the browser extensions you install and act on accordingly.
See below image for a popular Chrome extension, Todolist, permissions allowing access to its web site:

But keep this in mind; if you do not trust the add-on, you may not want to run it in the first place. We recommend you click the Remove button to delete any extension you do not trust. See following image:
That’s it. Please feel free to share this post! One way to share is via Twitter.
Just click the Tweet icon below. This will launch Twitter where you click its icon to post the Tweet.
Check our TechSavvy.Life for blog posts on smartphones, PCs, and Macs! You may email us at contact@techsavvy.life for comments or questions.
Tweet
I Would Like to Hear From You
Please feel free to leave a comment. I would love hearing from you. Do you have a computer or smart device tech question? I will do my best to answer your inquiry. Just send an email to contact@techsavvy.life. Please mention the device, app and version that you are using. To help us out, you can send screenshots of your data related to your question.


